Have you ever wondered how what seems like an ordinary coding oversight could open a gateway to disastrous cyber exploits? It might sound like the plot of a thrilling novella, but in recent developments, this scenario has become a stark reality in the cybersecurity world.

Understanding the Vulnerability
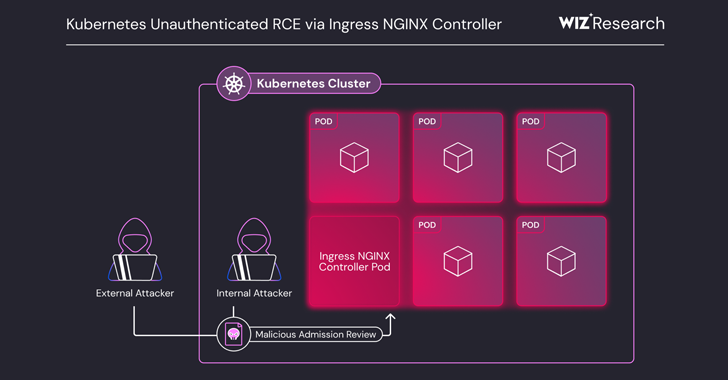
In the ever-evolving landscape of technology and cybersecurity, the discovery of a critical vulnerability in the Ingress NGINX Controller for Kubernetes has set alarm bells ringing. This Achilles’ heel isn’t just a minor hiccup; it’s a massive security flaw with the potential to wreak havoc on digital systems across the globe. Imagine the nerve-wracking possibility of remote code execution (RCE) happening on your IT infrastructure without the battlements of authentication to protect you.
What is the Ingress NGINX Controller?
First, a quick brush-up on what we’re dealing with here. The Ingress NGINX Controller is a popular tool used to manage external access to services in a Kubernetes cluster. Essentially, it functions as a bridge connecting your services with external users by mapping HTTP and HTTPS requests to applications within the cluster. Kubernetes, if you’re unfamiliar, is akin to the maestro of the orchestration space—managing containerized applications across a cluster of machines.
The Heart of the Vulnerability
This alarming vulnerability was disclosed on March 24, 2025, revealing five critical security shortcomings deeply embedded within the Ingress NGINX Controller for Kubernetes. These shortcomings can enable unauthenticated RCE, leading to potential unauthorized access to all secrets stored across Kubernetes clusters. Talk about a digital Pandora’s box!
Vulnerability Details: Ominously Named “IngressNightmare”
A Slew of Vulnerabilities
The security glitches are not willy-nilly incidents of coding gone awry but a collection of critical issues, ominously codenamed “IngressNightmare” by the cyber sentinels at cloud security firm Wiz. With a staggering CVSS score of 9.8, these vulnerabilities are:
- CVE-2025-24513, CVE-2025-24514, CVE-2025-1097, CVE-2025-1098, and CVE-2025-1974
These nefarious codings do not impact the NGINX Ingress Controller, a separate ingress tool used for NGINX and NGINX Plus, but remain a glaring threat for many.
The Root Cause
At the core, this vulnerability affects the admission controller component of the Ingress NGINX Controller, exposing over 6,500 clusters to risks on the public internet. The real mastermind behind the vulnerability? Admission controllers with haphazard network access sans authentication, sneaking in like a bandit hitching a ride with your HTTP traffic.
Configuration Misuse
Attackers exploit this flaw by injecting arbitrary NGINX configurations remotely. This sinister game plan involves sending malicious ingress objects—known as AdmissionReview requests—directly to the admission controller. The result? The Ingress NGINX Controller’s pod falls prey to code execution attacks.

The Exploit in Action
A Recipe for Disaster
To better understand the scale of the attack, imagine you’re a threat actor (a fancy term for someone up to no good in the cyber realm). You slyly upload a malicious payload as a library to the pod using NGINX’s client-body buffer. Then, you send an AdmissionReview request to the exposed admission controller, exploiting one of the aforementioned configuration directive injections. The outcome? The rogue library loads, inviting RCE into your domain as if it were drawing room theatrics.
Command over Clusters
The malicious streak doesn’t just stop at executing arbitrary code. With the admission controller’s elevated privileges, hackers can access all cluster secrets—spread across namespaces—culminating in a potential cluster takeover, like a digital kingpin claiming absolute control.

The Aftermath and Countermeasures
Wiz’s Warning
The intrepid researchers at Wiz warned that these vulnerabilities present an unlawful passport to perpetrators to pry and pilfer secrets stored on the cluster. Ever seen the anxious shudder run down an IT professional’s spine? Yeah, that’s the moment.
Responsible Disclosure and Remediation
Relief came post-disclosure as the vulnerabilities were rectified in the newer versions of the Ingress NGINX Controller: 1.12.1, 1.11.5, and 1.10.7. Hats off to those prompt patchwork knights saving the day!
Recommendations and Mitigation
To protect against such stealthy cyber invasions, consider these strategic countermeasures:
-
Update Promptly: Upgrade to the latest versions of the Ingress NGINX Controller—procrastination is not a luxury you can afford in cybersecurity.
-
Shield the Admission Controller: Ensure it isn’t exposed externally—lock up those kingdom gates!
-
Access Limitation: Limit the Kubernetes API Server’s access to the admission controller as a snug layer of protection.
-
Temporary Disabling: If not essential, temporarily disable the admission controller component to prevent exploitation.

Reflecting on the Cybersecurity Landscape
A Peep into the Outcome
The worrying tale of the Ingress NGINX Controller vulnerability reminds us of the cyber battleground we navigate today. Does it appear overly dramatic to contemplate vulnerabilities with such significance? It shouldn’t. With evolving tech ecosystems come intricate entanglements that reshape our understanding and approach to cybersecurity.
Broadening the Horizon
More than an isolated quirk, this vulnerability underscores the gaps in system security. It’s a clarion call for a proactive, not reactive, approach to defending our digital bastions.
A Dress Rehearsal for Disaster Preparedness
This incident presents an opportunity—a chance to refine disaster response strategies beforehand, ensuring systems are prepared and resilient enough to outlive such cyber mishaps. Are your disaster recovery plans as robust and foolproof as you envision?

Conclusion: Embracing a Resilient Future
Cybersecurity is a domain perpetually on its toes. As we exploit technology for greater leeway and innovation, we must stay vigilant, remembering each vulnerability is an invitation to bolster defenses and refine our strategies. Whether you’re tech-savvy or exploring the edges of this universe, understanding and anticipating these challenges empower us to shape a future that is both innovative and secure.